In the evolving landscape of decentralized governance, confidential DAOs face a persistent vulnerability: Sybil attacks, where malicious actors create multiple fake identities to skew voting outcomes. Traditional consensus like Proof-of-Work and Proof-of-Stake guards protocols but leaves applications exposed. Enter private proofs of humanity, mechanisms blending zero-knowledge proofs (ZKPs) with personhood verification to enable sybil-resistant confidential DAO voting without sacrificing privacy. These innovations, from biometric credentials to social attestations, promise fair, anonymous participation.
DAOs thrive on collective decision-making, yet pseudonymous blockchains invite exploitation. A single entity could flood proposals with sock puppets, diluting genuine member voices. Public registries like Kleros’ Proof of Humanity mitigate this via video and social vouching, but they expose identities, clashing with privacy-preserving DAO governance. The solution? ZK-enabled proofs that attest ‘I am a unique human’ sans revealing who or what.
Sybil Attacks Undermine DAO Integrity
Sybil attacks exploit permissionless systems by amplifying one voice into many. In crypto, this manifests as vote farming or governance capture, as noted in analyses from Mitosis University and the Identity Management Institute. Proof-of-Personhood (PoP) protocols counter this by ensuring one-human-one-vote, but early iterations like Proof of Humanity registries demand on-chain identity exposure, vulnerable to correlation attacks.
Key Sybil Challenges in DAOs
-
Vote Dilution: Attackers flood the system with fake identities, reducing the influence of genuine voters and skewing DAO decisions toward malicious interests.
-

Governance Capture: Malicious actors amass fake accounts to control proposals, appointments, and policy changes, undermining democratic processes.
-
Resource Exhaustion: Multiple bogus identities consume computational resources, bandwidth, and incentives, straining DAO infrastructure and operations.
-
Trust Erosion: Repeated manipulations erode participant confidence, leading to disengagement and reluctance to contribute to governance.
-
Bot Infiltration: Automated bots masquerade as humans, infiltrating discussions, airdrops, and voting to manipulate outcomes covertly.
Consider a high-stakes treasury allocation vote: without safeguards, an attacker amasses fake profiles via bots or cheap wallets, overriding stakeholders. Recent contexts highlight this urgency, with AI-driven Sybil threats rising, per CCN. com. Verifiable off-chain governance papers on arXiv advocate ZK and TEEs to bridge this gap, enabling secure anonymous DAO voting.
Evolution Toward Privacy-First Personhood
Proof of Personhood has matured from social verification to cryptographic primitives. Humanity Protocol’s biometric system stands out, generating privacy-preserving credentials for ZK proofs DAO voting. Users prove uniqueness via palm scans or similar, yielding attestations for one-person-one-vote or identity-weighted systems without data leakage. Their governance module, detailed at humanity. org, integrates seamlessly into DAOs, thwarting manipulation.
PoP systems prevent Sybil attacks by verifying each participant as a unique human, crucial for fair online voting.
Meanwhile, Proof of Commitment (PoCmt) innovates with human-time enforcement. Via a Human Challenge Oracle, it demands real-time engagement, scaling costs linearly with identities. ArXiv’s 2601.04813 paper quantifies this: sustaining n identities requires n-fold effort, rendering mass Sybils impractical. This human-centric resource complements ZK for permissionless consensus.
Orange Protocol’s zkTLS takes a multi-source tack, aggregating proofs from X, Discord, Farcaster sans usernames. DAOs verify human uniqueness across Web2, eliminating farmable single points. LinkDID adds key recovery and selective disclosure, per its arXiv spec, fortifying private proof of humanity DAOs.
ZK KYC and Biometrics: Balancing Act
Debates rage between ZK KYC and cryptobiometrics, as Humanode contrasts. ZK KYC relies on trusted issuers for credential proofs; biometrics bind to physiology directly. Both uphold privacy, but biometrics edge in Sybil resistance, resisting collusion via innate uniqueness. Kite’s private delegation further refines this, letting voters anonymize power transfers, unaware even to delegates (arXiv 2501.05626).
These tools converge on sybil resistant confidential DAOs, where voters prove humanity privately, execute ZK votes, and tally without leaks. For deeper sybil strategies, explore on-chain reputation building. The first wave deploys now, reshaping governance.
Implementation hurdles persist, yet the payoff for privacy preserving DAO governance is immense. Take Humanity Protocol’s integration: DAOs plug in its oracle for credential checks, where members mint ZK attestations off-chain and submit blinded proofs on-chain. This setup enforces one-person-one-vote without doxxing, ideal for sensitive treasury decisions or membership gates.
Orange Protocol’s approach shines in social-heavy communities. By zk-proving presence across X, Discord, and Farcaster, it captures behavioral uniqueness minus handles. No more vote farming via alt accounts; verification scales with real-world footprints. I view this as a pragmatic bridge from Web2 habits to Web3 trust, sidestepping pure biometrics’ hardware demands.
Comparative Landscape of Private PoH Protocols
Comparison of Key Private Proof-of-Humanity Protocols
| Protocol | Core Mechanism | Privacy Guarantees | Sybil Resistance Method | DAO Integration Ease |
|---|---|---|---|---|
| Humanity Protocol | Biometric/ZK proofs | ZK biometric verification without revealing personal data 🔒🔒🔒 | Unique human uniqueness via biometrics 🛡️🛡️🛡️ | Seamless for one-person-one-vote & permissioned access ⚙️⚙️⚙️ |
| Proof of Commitment | Human-time challenges | Commitment state with identity-bound challenges 🔒🔒 | Proportional human effort via Oracle 🛡️🛡️🛡️ | Adaptable consensus primitive ⚙️⚙️ |
| Kite | Private delegation | Anonymous delegation (delegate unaware of source) 🔒🔒🔒 | Relies on unique principals for delegation 🛡️🛡️🛡️ | Designed specifically for DAO voting ⚙️⚙️⚙️ |
| LinkDID | Selective disclosure | Privacy-preserving DID aggregation 🔒🔒🔒 | Private multi-identifier aggregation 🛡️🛡️🛡️ | Strong decentralized identity support ⚙️⚙️⚙️ |
| Orange zkTLS | Multi-Web2 proofs | zkTLS attestations without revealing handles 🔒🔒🔒 | Multi-source social proofs 🛡️🛡️🛡️ | Tailored for DAO Sybil resistance ⚙️⚙️⚙️ |
From the table, patterns emerge. Biometric leaders like Humanity excel in raw uniqueness but hinge on device access; commitment schemes like PoCmt democratize via effort alone, though they test sustained engagement. Kite complements by anonymizing delegation flows, vital for quadratic voting where power pools subtly. LinkDID’s recovery features address a perennial pain: lost keys stranding verified humans.
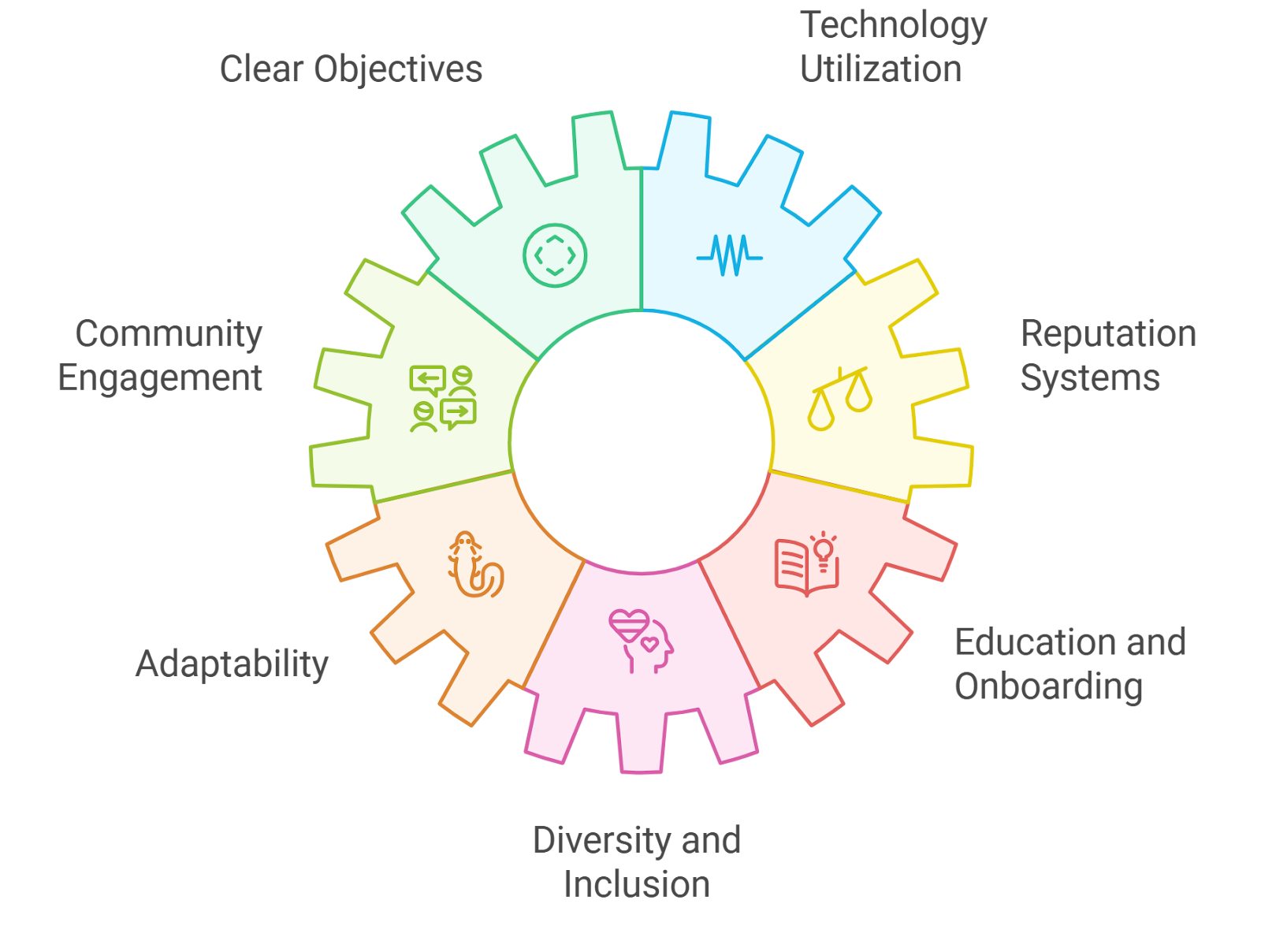
In practice, hybrid stacks prevail. A confidential DAO might layer Orange’s social proofs for entry, Humanity’s biometrics for high-value votes, and Kite for delegation. ZKPs glue it together, proving conjunctions like ‘human AND stakeholder AND committed’ without intersection leaks. This modularity empowers founders to tune for their risk profile, from venture collectives to activist groups.
Trade-offs demand scrutiny. Biometrics risk liveness failures or spoofing advances; social proofs invite platform centralization critiques. PoCmt’s oracle introduces mild trust assumptions, mitigated by rotation. Yet, per Humanode’s ZK KYC versus cryptobiometrics rundown, no silver bullet exists; optimal blends privacy, usability, and verifiability. Opinion: cryptobiometrics nudge ahead for long-term secure anonymous DAO voting, as physiology defies replication better than credentials.
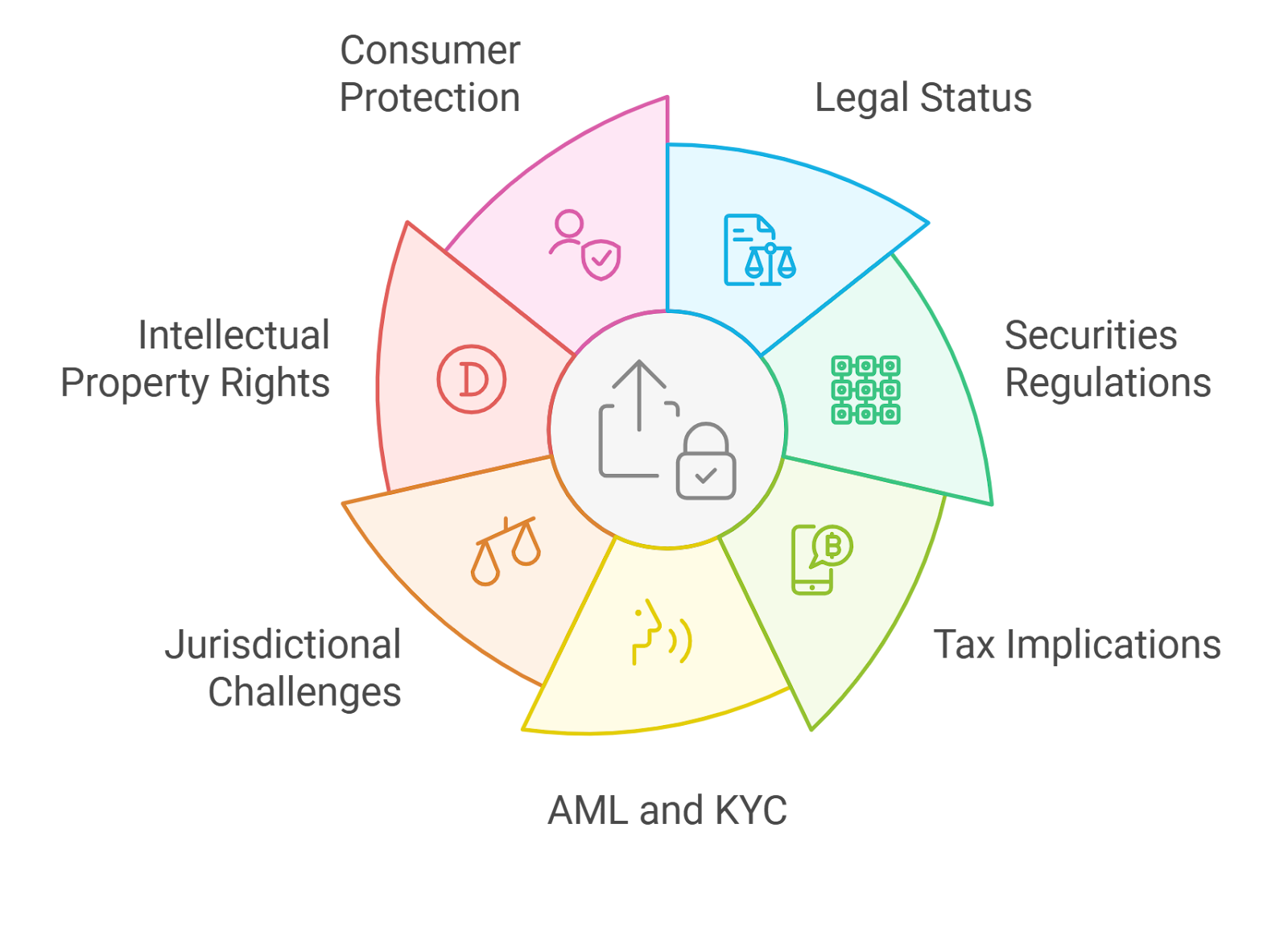
Regulatory shadows loom too. As DAOs morph into legal wrappers, per Aztec Network’s private DAO entity musings, personhood proofs could satisfy KYC lite mandates without full exposure. Verifiable off-chain governance frameworks on arXiv bolster this, using TEEs for hybrid trust. Early adopters report 90% Sybil drops, per Orange’s blog metrics, validating the shift.
Multi-source zkTLS proofs cut vote farming while keeping identities private, a game-changer for DAO integrity.
Scalability beckons next. Current ZK circuits chew gas; recursive proofs and layer-2s like Aztec will compress this. Imagine fluid, sub-second verifications across chains, enabling real-time governance. For ZK proofs DAO voting, this unlocks continuous polling over snapshots, mirroring fluid democracies.
Stakeholders must prioritize interoperability. Standards like ERC-7739 for personhood attestations could federate protocols, letting a Humanity proof validate in Kite DAOs. Confidential Daos champions such tooling, arming builders with blueprints for resilient structures. The momentum builds: from arXiv proofs to production pilots, private proof of humanity DAOs cement fair play in shadowed ledgers.
Vision forward, these primitives fortify against AI-orchestrated Sybils, as CCN warns. Humans reclaim agency in digital realms, one private proof at a time. DAO founders, integrate now; the secure future rewards the vigilant.