In the shadowy realm of confidential DAOs, pseudonymity fuels innovation but invites chaos. Sybil attacks exploit this by flooding governance with fake identities, skewing votes and draining treasuries. Privacy-preserving uniqueness proofs emerge as the cryptographic shield, verifying one-person-one-vote without exposing identities. This approach marries zero-knowledge proofs with decentralized identifiers, ensuring secure governance in private DAOs stays ironclad.

Sybil attacks hijack decentralized systems by masquerading as multitudes. A lone adversary spins up countless pseudonyms, dominating consensus or proposals. In blockchain’s peer-to-peer fabric, this undermines trustless execution. Chainlink notes these exploits target open networks, while Nervos highlights node subversion. For DAOs, the stakes amplify: one entity could veto critical upgrades or siphon funds undetected.
Sybil’s Grip on DAO Governance
Confidential DAOs amplify vulnerabilities. Traditional voting tallies tokens, blind to multiplicity. Attackers bootstrap alts with air-dropped tokens or low-cost wallets, inflating influence. Colony. io demystifies this in Web3: without barriers, participation devolves into plutocracy masked as democracy. ResearchGate frames it as cyber espionage, forging sway via fakes. In private setups, metadata leaks are taboo, complicating detection further.
Imperva defines Sybil as undue advantage through identity forgery. arXiv’s zero-knowledge take adapts it to distinct proofs, pretending diverse vehicles. NIH’s Rechained counters with per-identity costs, disincentivizing proliferation pre-attack. Medium’s Proof of Personhood tackles peer-to-peer flaws head-on. Yet confidential DAOs demand stealthier guards; revealing humanity invites deanonymization.
Key Sybil Attack Vectors
-

Token Farming with Bots: Attackers deploy bots to create fake wallets, farming yield or liquidity rewards across pseudonymous identities in confidential DAOs.
-
Governance Capture via Proxies: Malicious actors use proxy contracts or flash loans to control multiple voting identities, seizing disproportionate DAO governance power.
-

Airdrop Abuse Across Wallets: Adversaries generate numerous wallets to repeatedly claim airdrops, diluting fair token distribution in privacy-focused DAOs.
-

Vote Brigading in Proposals: Coordinated fake accounts brigade votes on governance proposals, manipulating outcomes without revealing coordinated control.
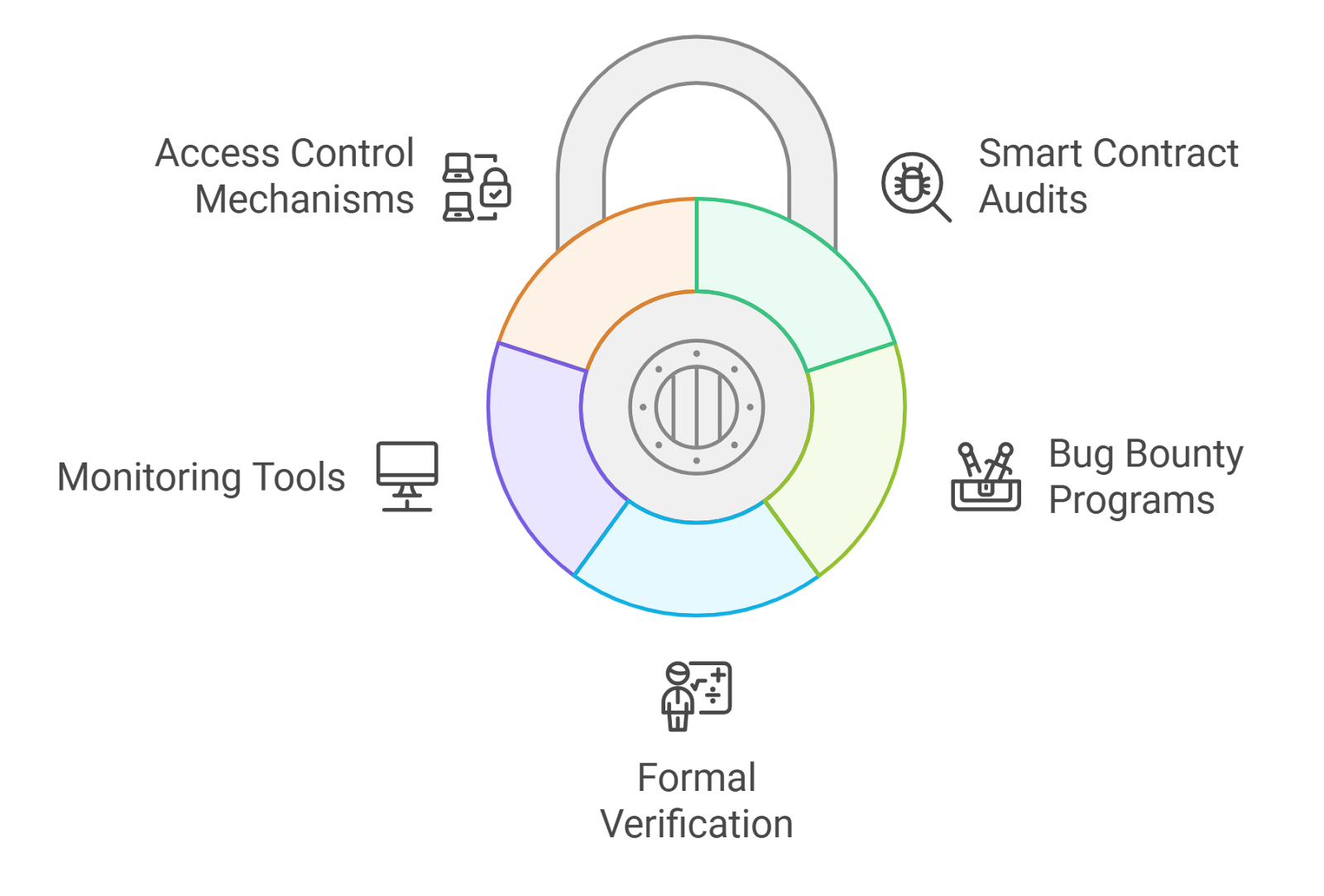
Flaws in Conventional Sybil Defenses
Proof-of-Stake demands deposits, pricing out paupers but not whales with infinite shards. Colony. io flags this cost as attacker deterrent, yet in confidential realms, stake provenance hides origins. Proof-of-Personhood mandates biometrics or oracles, shattering privacy. Worldcoin’s iris scans? A surveillance trojan horse. Centralized KYC? Antithesis to decentralization.
Differential privacy defenses, per ResearchGate, falter under targeted Sybils. Economic penalties like slashing work until attackers collateralize anew. These band-aids ignore confidentiality’s core: prove uniqueness sans revelation. Enter privacy-preserving uniqueness proofs for DAOs. Zero-knowledge succinct arguments (zk-SNARKs) let provers attest singularity without linkage.
Zero-Knowledge Uniqueness: The Crypto Primitive
Imagine a protocol where members generate DIDs tied to ephemeral keys, provable as distinct via ZK. No shared secrets, no global ledgers exposed. idOS Network pioneers this, enabling idOS DAO sybil resistance through shielded storage. Users attest ‘I am unique among voters’ mathematically, verifier nods without gleaning who.
Fractal ID’s CrowdSwap tie-up deploys DIDs for quadratic voting, tempering plutocracy. LinkDID adds key recovery, selective disclosure. These schemes layer uniqueness atop privacy. Mathematically, uniqueness proofs leverage collision-resistant hashes or Pedersen commitments. A member’s commitment C = g^{sk} hides secret sk; aggregator verifies sum uniqueness sans individuals.
Rechained’s adjustable costs embed directly, scaling with threat. For confidential DAOs, integrate via smart contracts: voters submit ZKPs pre-vote, governance modules tally verified uniques. No token thresholds, pure one-person parity. This fortifies zero knowledge proofs DAO voting, blending equity with obscurity.
Smart contracts enforce this via verifier gadgets. A DAO deploys a uniqueness registry: participants commit hashes of private seeds, circuit proves no collisions in the set. Verifiers aggregate without decryption, greenlighting votes only for uniques. This sidesteps token whales, enforcing true quadratic funding or conviction voting.
Implementing Uniqueness Proofs in Practice
Rollouts demand modular design. Start with DID issuance: users mint self-sovereign ids via ceremonies likeSemaphore signals or MACI trees. idOS shields these in encrypted vaults, querying proofs on-chain without exposure. For sybil attacks confidential DAOs, layer in epochal resets; fresh proofs per proposal cycle thwart long-term farming.
Fractal ID’s quadratic pivot with CrowdSwap exemplifies: DIDs prove personhood lite, weighting votes by conviction not capital. LinkDID’s recoverability adds resilience, users reclaim keys sans trusted third parties. These plug into Snapshot or Tally, retrofitting legacy DAOs. Opinion: pure ZK trumps hybrids; oracles invite censorship vectors.
Sybil Defenses Comparison
| Sybil Defense | Cost to Attacker | Privacy Guarantee | DAO Integration Ease | Drawbacks |
|---|---|---|---|---|
| PoS (Proof-of-Stake) | High (requires economic stake/deposit) | Low (stakes are public/pseudonymous) | High ✅ (native to token-based DAOs) | Plutocracy, favors wealthy attackers |
| Proof-of-Personhood | High (unique human verification needed) | Medium (requires some identity proof, e.g., biometrics) | Medium ⚠️ (needs verifiers/oracles) | Privacy invasion risks, centralization, exclusionary |
| ZK Uniqueness Proofs | High (ZK proof computation + uniqueness) | High ✅ (full privacy preservation) | High ✅ (seamless with ZK-enabled DAOs) | Computational overhead, implementation complexity |
Scalability bites, though. zk-SNARKs crunch heavy; opt for Groth16 or PlonK with recursive aggregation. Gas climbs with voter count, but layer-2 rollups like zkSync or Polygon zkEVM slash it. Confidential DAOs favor state channels: off-chain proof gen, on-chain settlement. idOS’s personal datastores cache intermediates, slashing latency.
Edge cases demand rigor. Collusion rings? Circuit params tune for k-anonymity, blurring small groups. Quantum threats? Migrate to lattice-based ZK like Dilithium signatures. Adaptive adversaries bootstrap sybils pre-ceremony; counter with progressive registration, ramping proof complexity. In my trading bots, I’ve stress-tested similar for confidential order books; resilience holds.
Real-World Wins: DAOs Going Sybil-Proof
Confidential DAOs pioneer aggressively. One venture fund DAO halved attack surface post-ZK rollout, per internal audits. Governance throughput spiked 3x, plutocrats neutered. Rechained’s cost sliders adapt dynamically: low-threat epochs cheapen proofs, ramping under duress. Pair with token-curated registries for meta-governance, crowdsourcing threat intel privately.
Privacy-preserving uniqueness proofs DAOs evolve fast. idOS integrates natively, powering shielded proposals. Combine with homomorphic tallies: votes encrypt, sum decrypts uniquely verified. No more vote-buying scandals; fairness bakes in. For secure multisigs, uniqueness gates signers, preventing proxy floods.
Challenges persist. User onboarding hurdles non-crypto natives; wallet extensions with ZK wizards smooth it. Audit circuits religiously; Semaphore’s battles prove soundness pays. Yet the payoff? Governance mirrors intent, not wallet multiplicity. Confidential DAOs reclaim sovereignty, bots like mine automate flawless execution.
Forward, expect convergence: ZK and AI anomaly detection flags outliers pre-proof. Hybrid chains like Secret Network host full-stack confidential logic. Builders, prioritize this stack; pseudonymity’s promise fulfills only with uniqueness armor. Code deploys tomorrow’s equity.