In 2026, decentralized autonomous organizations handling sensitive data face unprecedented scrutiny. Public blockchains expose every transaction, vote, and treasury move, inviting coercion, leaks, and regulatory pitfalls. Confidential DAOs flip this script with cryptographic tools that lock down sensitive data governance while preserving verifiability. Drawing from Oasis Protocol's push for confidential computing and the Confidential Computing Consortium's white paper on data integrity, these setups treat data as the ultimate asset in Web3's transparent minefield.
Zero-Knowledge Proofs: Verifying Without Revealing
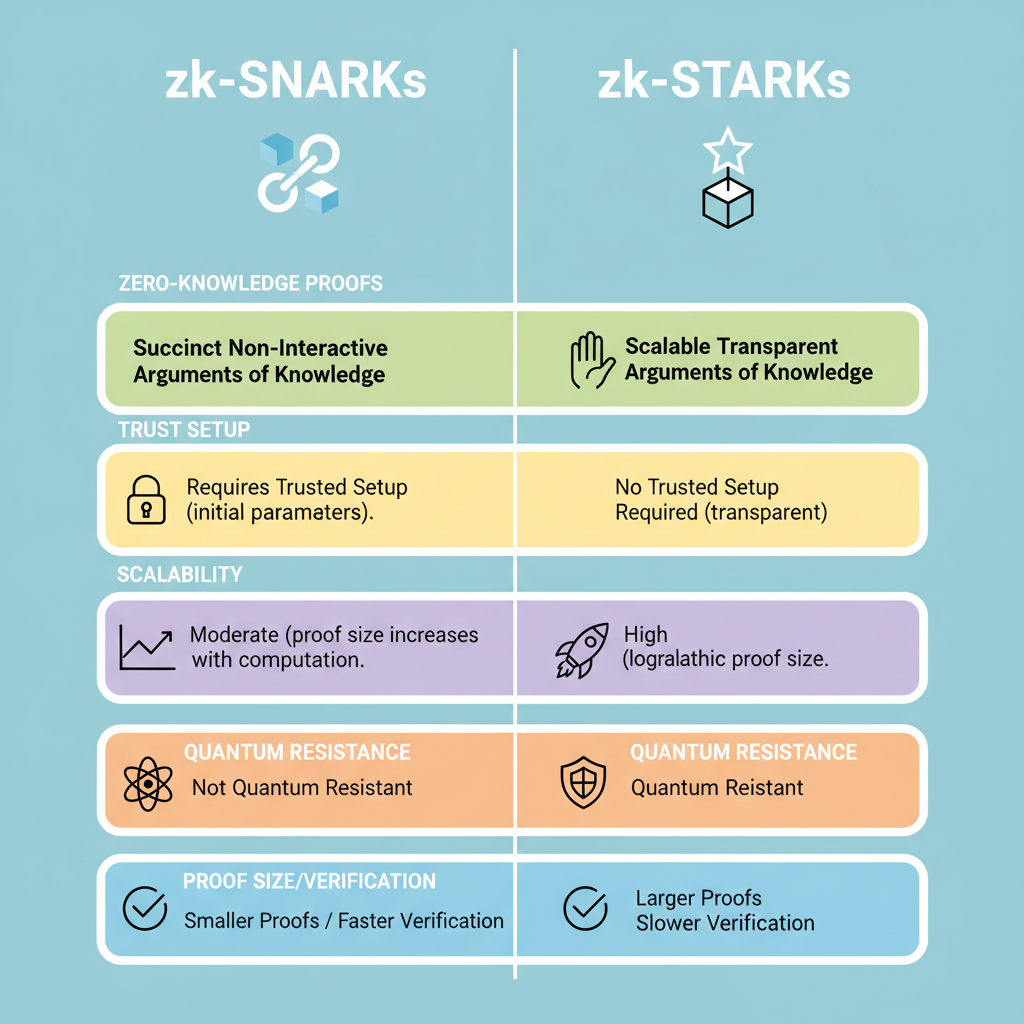
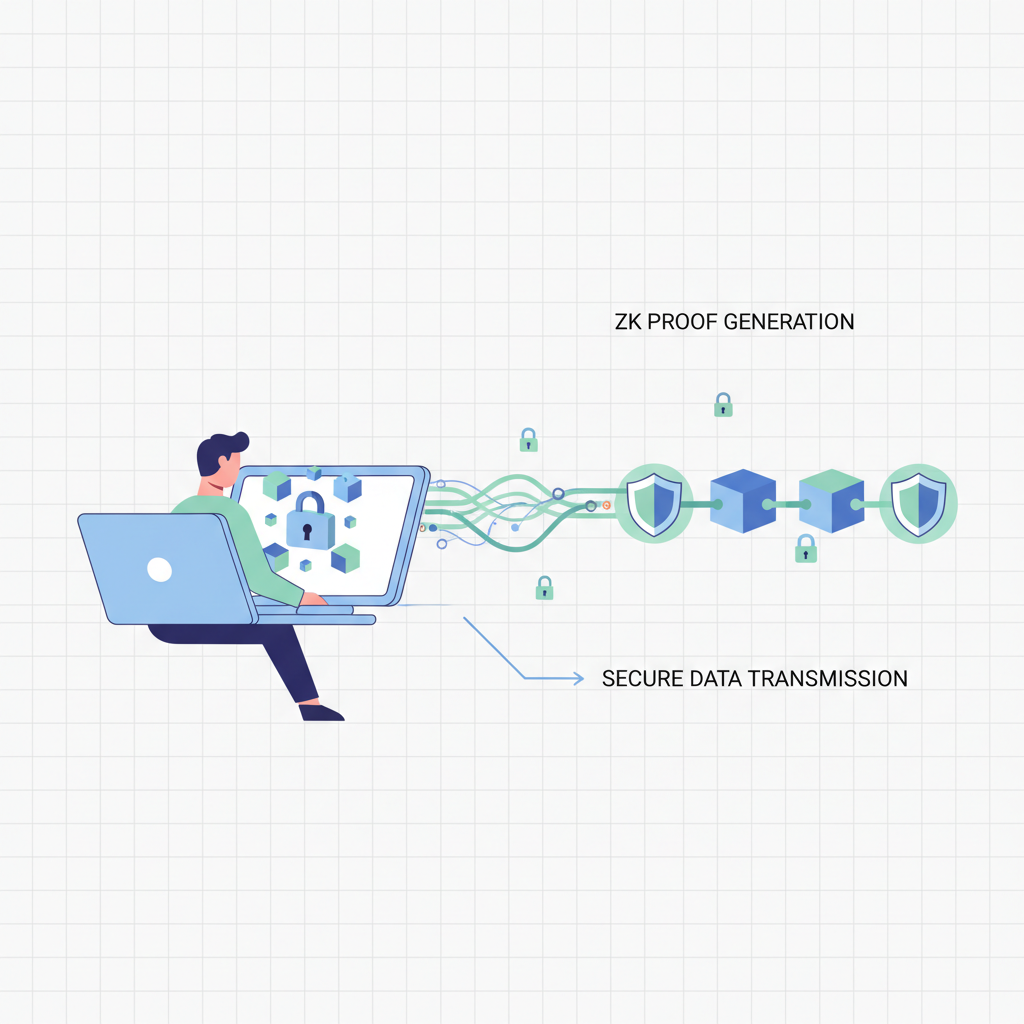
Zero-Knowledge Proofs (ZKPs) stand as the cornerstone of ZK proofs DAOs. They let members prove a vote's validity or a transaction's legitimacy without leaking details. CimCo Tech highlights ZKPs managing tax info and voter rolls securely; in DAOs, this scales to confidential proposals and treasury audits. ZK-SNARKs offer compact proofs for speed, while ZK-STARKs prioritize transparency without trusted setups. Panther Protocol's exploration of ZKPs in Web3 underscores their role in shielding user privacy amid public chains.
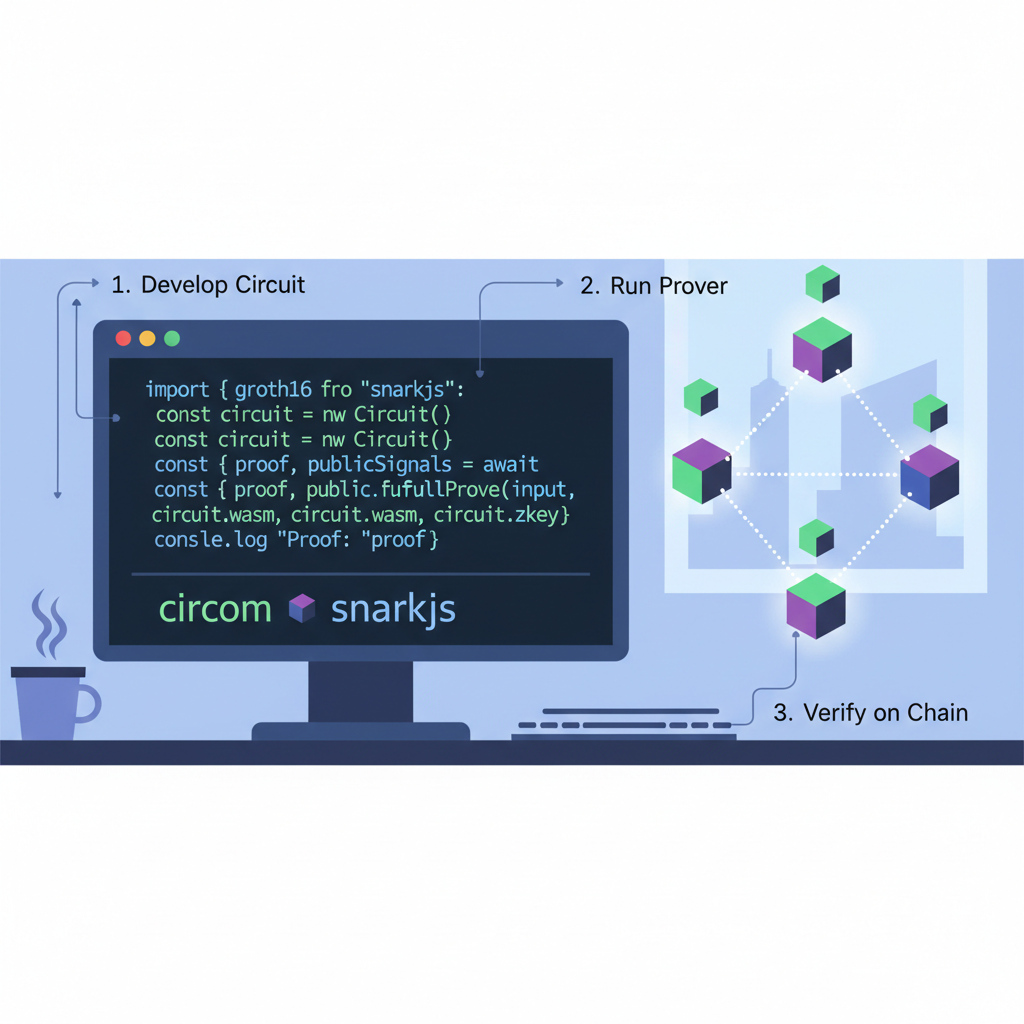
Termina on Solana exemplifies this with zkSVM Prover, enabling private computations verified on-chain. For DAO founders, integrate ZKPs via libraries like circom or halo2. Start small: prove token balances exceed a threshold for voting eligibility without exposing holdings. This balances secure DAO governance with participation.
Fully Homomorphic Encryption and TEEs for Compute Privacy
Beyond proofs, Fully Homomorphic Encryption (FHE) allows computations on ciphertexts. Tally votes or analyze treasury yields encrypted end-to-end. Onchaintreasury. org details FHE for confidential DAO treasury management, preventing exposure during financial ops. Pair it with Trusted Execution Environments (TEEs) like Oasis Sapphire, where smart contracts run in hardware enclaves, shielding code and data from even node operators.
The Association for Computing Machinery praises ZKPs for confidential data computations, but FHE and TEEs extend this to full workflows. Binance calls ZK the holy grail of privacy; confidential computing amplifies it. Deploy TEEs for high-stakes DAOs dealing with IP or health data, ensuring DAO privacy tools hold against insider threats.
ArXiv's zk-agreements protocol merges legal enforceability with crypto privacy, ideal for sensitive data DAOs. Prototype with FHE libs like TFHE-rs on Rust chains.
Best Practices: Locking In Anonymous Voting and Delegation
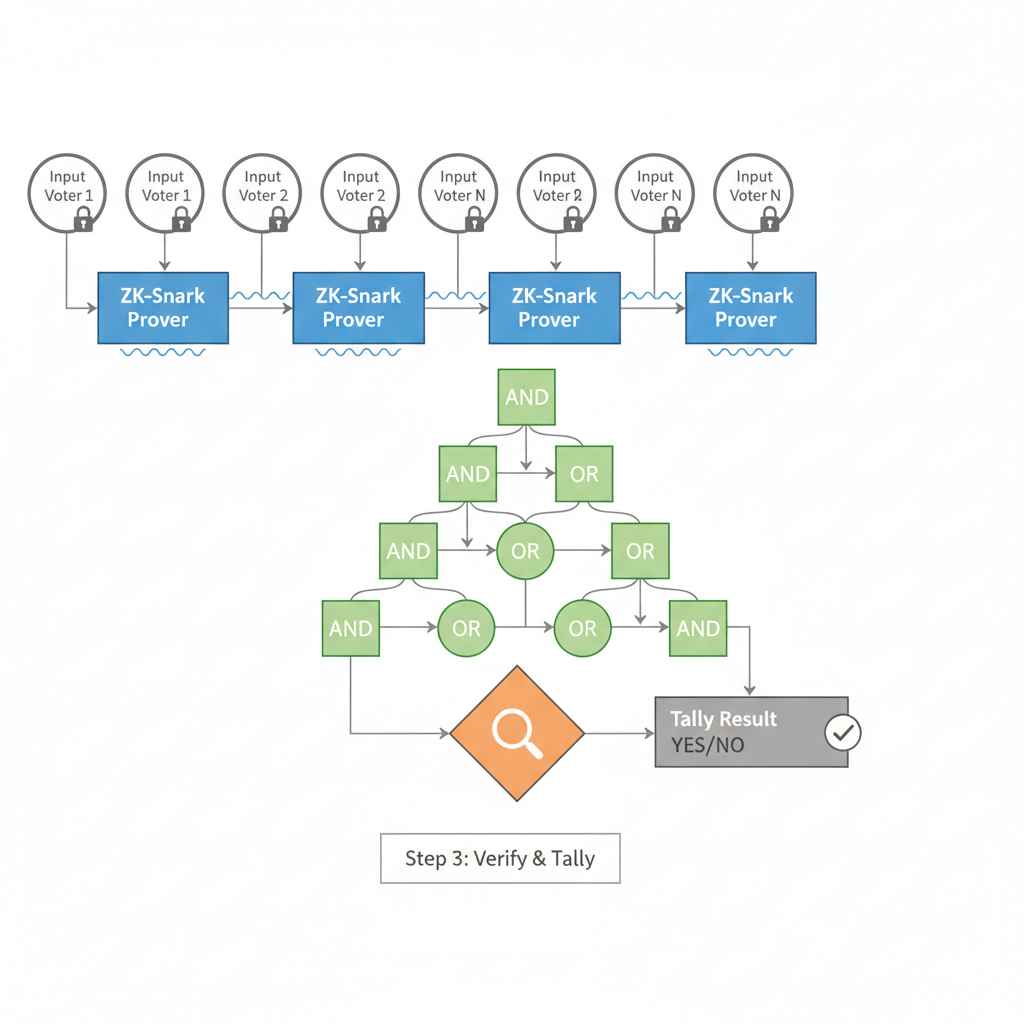
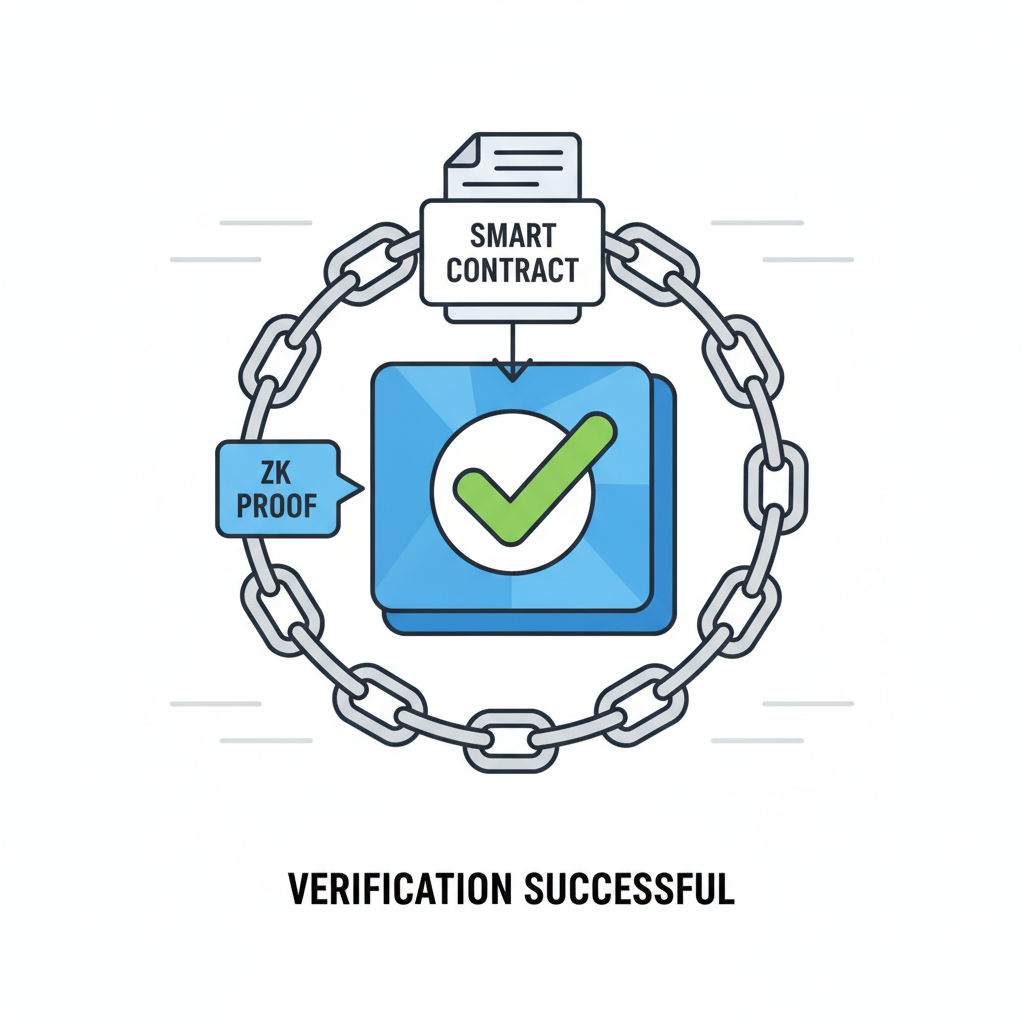
Tools alone falter without protocols. Anonymous voting curbs vote-buying; implement via ZKPs where proofs confirm eligibility sans identity. Confidentialdaos. com outlines this for private governance. Private delegation lets members assign power blindly, boosting flexibility without graph analysis risks.
Confidential proposal creation invites ideas sans retaliation fears. For treasury privacy, use FHE to obscure strategic moves yet audit via ZK receipts. Select ZKP variants per needs: SNARKs for gas efficiency, STARKs for quantum resistance. Test in staging: simulate 1,000 votes, measure latency under 10 seconds.
GoCodeo AI notes ZKPs make public chains enterprise-ready. In practice, layer these atop Ethereum L2s or Solana for cryptographic solutions DAOs. Monitor gas costs; optimize circuits iteratively. This stack empowers DAOs to govern health records, NDAs, or venture deals confidentially.
Layering these confidential compute blockchain primitives demands rigorous testing. Run adversarial simulations: attempt deanonymization via timing attacks or chain analysis. Tools like Panther Protocol's privacy mixers complement ZKPs, obfuscating flows before proof submission.
Treasury Management: Shielding Assets in Plain Sight
DAO treasuries hold the real stakes - venture allocations, IP licenses, or health consortium funds. Public visibility invites front-running; confidential setups change that. FHE computes yield optimizations on encrypted balances, revealing only aggregate outcomes. Oasis Sapphire's TEEs attest to execution integrity, letting auditors verify without decryption keys. The Confidential Computing Consortium's white paper nails it: this slashes insider risks, vital for sensitive data DAOs.
Comparison of ZKP Variants for DAOs
| Type | Proof Size | Trust Setup | Quantum Resistance | Gas Cost | Use Case |
|---|---|---|---|---|---|
| ZK-SNARK | Compact | Yes | Low | Low | Voting |
| ZK-STARK | Large | No | High | High | Treasury |
Integrate via modular contracts: a ZKP mixer for inflows, FHE oracle for analytics. Confidential treasury protocols ensure moves stay dark until execution, auditable post-facto. I've seen DAOs lose millions to leaked strategies; this stack prevents it.
Overcoming Implementation Hurdles
Gas bloat and proof times trip up newcomers. Optimize with recursive proofs or L2 rollups. Solana's Termina cuts latency for high-throughput votes. Audit circuits third-party; Semaphore or Tornado Cash forks provide battle-tested primitives. For FHE, threshold schemes distribute keys across multisigs, dodging single points of failure.
Legal angles matter too. zk-agreements bind enforceability cryptographically, per arXiv's blueprint. Pair with off-chain oracles for real-world data feeds, ZK-verified. This isn't theory; health DAOs tally patient consents privately, venture groups screen deals sans leaks.
Challenges persist: FHE's compute overhead demands GPU clusters, ZKPs require circuit expertise. Mitigate with SDKs like ZoKrates or Concrete-ML. Start hybrid: TEEs for core logic, ZKPs for verifiability. Scale via optimistic execution, settling disputes confidentially.
By 2026, expect zkEVMs mainstreaming these natively. FHE-TEE hybrids will dominate enterprise DAOs, per GoCodeo AI's enterprise pivot. Founders, prototype now: fork a governance contract, layer Semaphore voting, deploy to testnet. Measure participation spikes - privacy breeds bold decisions. Secure DAO governance isn't optional; it's the edge in Web3's data wars.







No comments yet. Be the first to share your thoughts!